Stop Malware
Before It Affects
Your Store
The only Magento 2 module that scans every uploaded file the instant it arrives — stopping malware before it reaches your store. No external service. No cloud. 100% on-premise.
- Works on Magento 2.4.x CE & EE
- Compatible with Adobe Commerce Cloud
- No external API calls — 100% on-premise
- Covers REST API uploads (PolyShell protected)
- Caught what Sucuri missed — proven on a live zero-day attack
Testimonials
Real feedback from teams who've had Malware Monitor catch live attacks.
Feature Comparison
| Feature | Shield | Shield Pro |
|---|---|---|
| Real-time upload scanning (all sources) | ||
| Pattern detection (eval, exec, base64, polyglot, obfuscation) | ||
| Admin malware alert modal | ||
| Auto-quarantine + management grid | ||
| Upload attempts log with forensic details | ||
| Email alerts on malware detection | ||
| Cron-based full store file scanning | ||
| Suspicious events log | ||
| Admin dashboard threat statistics | ||
| Content threat scanning (CMS, products, categories, widgets, email templates, design & system config) | ||
| Content threat — block on detection | ||
| Database content scanning — CMS pages, blocks, email templates, store config | ||
| IP Firewall — whitelist / blacklist | ||
| Auto-block IP on detection threshold | ||
| CLI tools (malware:scan, monitor, analyse, check, db-scan, test-email) | ||
| Directory extension statistics | ||
| Owner-candidate file detection | ||
| Settings change audit log | ||
| Per-user config password protection | ||
| Number of Domains | 1 | 3 |
| Priority Support | ||
| Price | $199/yr | $499/yr |
Simple, Transparent Pricing
Annual subscription · All updates included · 30-day money-back guarantee.
Need more than 10 domains? Contact us for enterprise pricing

Shield
Real-time protection for a single store
- Real-time upload scanning — all sources (product, category, media gallery, swatch, PageBuilder, REST API)
- Pattern detection: eval, exec, base64, obfuscation, polyglot files
- Admin malware alert modal on every upload
- Auto-quarantine + quarantine management grid
- Upload attempts log with forensic details (IP, user agent, MIME, endpoint)
- Email alerts on malware detection
- Cron-based full store file scanning
- Suspicious events log
- Admin dashboard threat statistics
- Content threat scanning (CMS, products, categories, widgets, email templates, design config, system config)
- IP Firewall — whitelist / blacklist
- Auto-block IP on detection threshold
- Content threat — block on detection
- Database content scanning
- CLI tools
- Directory extension statistics
- Owner-candidate file detection
- Excluded extensions configuration
- Settings change audit log
- Per-user config password protection
- Priority support

Shield Pro
Full protection + advanced controls
- Real-time upload scanning — all sources (product, category, media gallery, swatch, PageBuilder, REST API)
- Pattern detection: eval, exec, base64, obfuscation, polyglot files
- Admin malware alert modal on every upload
- Auto-quarantine + quarantine management grid
- Upload attempts log with forensic details (IP, user agent, MIME, endpoint)
- Email alerts on malware detection
- Cron-based full store file scanning
- Suspicious events log
- Admin dashboard threat statistics
- Content threat scanning (CMS, products, categories, widgets, email templates, design config, system config)
- IP Firewall — whitelist / blacklist
- Auto-block IP on detection threshold
- Content threat — block on detection
- Database content scanning
- CLI tools
- Directory extension statistics
- Owner-candidate file detection
- Excluded extensions configuration
- Settings change audit log
- Per-user config password protection
- Priority support
Compare to Sansec eComscan at €1,380+/year for an external service. Malware Monitor is native, on-premise, and costs less than a single month of their service.
How Malware Monitor Compares
Last verified: April 2026
| Feature | Malware Monitor | Mageplaza Security | Amasty Security Suite | Sucuri | Sansec eComscan | cside.com |
|---|---|---|---|---|---|---|
| Intercepts uploads before affect your store | cside monitors JS in the browser — cannot intercept PHP file uploads on the server |
|||||
| Blocks PolyShell / CVE-2024-39397 | Sucuri's WAF missed the live PolyShell CVE-2024-39397 zero-day attack in the wild |
cside only monitors client-side JS — server-side PHP exploits like PolyShell are out of scope |
||||
| File content analysis (not just hash/extension) | Sucuri scans files already on your server — detects infection after the fact, cannot prevent upload |
cside analyzes JS execution in browser — cannot inspect PHP file contents on the server |
||||
| Entropy-based obfuscation detection | cside detects JS obfuscation in browser scripts — not server-side PHP obfuscation or polyglot files |
|||||
| REST API upload protection | cside has no server-side component — REST API file uploads bypass it entirely |
|||||
| File change monitoring | Available in Mageplaza Security Pro only — not included in the free or standard edition |
External HTTP polling every 12–30 min — attacker has a window before detection triggers |
||||
| Quarantine & admin UI | Can flag files but lacks bulk actions, restore workflow, and real-time admin alerts |
No auto-quarantine — submit a cleanup request to Sucuri's team, resolved in hours |
CLI-only detection, no Magento admin quarantine panel or one-click restore |
Browser-side tool only — monitors JS execution, cannot quarantine or remove server-side files |
||
| IP blacklist / whitelist | IP rules available in Mageplaza Security Pro only — basic edition has no firewall controls |
|||||
| 2FA + admin login protection | ||||||
| CLI tools | ||||||
| 100% on-premise (no external API) | Sucuri is a cloud WAF — your traffic routes through their servers, adding latency and an external dependency |
Sansec eComscan is a cloud SaaS — file metadata is sent to external servers for analysis |
cside.com is cloud-based — JS execution data is processed on their platform, not on your server |
|||
| Client-side JS monitoring (browser skimmer detection) | Malware Monitor protects server-side file uploads and PHP code — client-side JS monitoring requires a complementary tool like cside |
Sucuri WAF blocks known JS patterns at HTTP layer — cannot monitor actual browser execution or detect novel skimmers |
||||
| Price | $199/yr | $99–149/yr | $319/yr | $229–549/yr | €1,380–6,900/yr | Free · $99/mo ($1,188/yr) |
Sansec eComscan scans files after they land on your server — it’s a post-infection forensics SaaS. Sucuri’s WAF operates at the HTTP layer and cannot inspect file contents. cside.com is a complementary client-side tool — it monitors JavaScript execution in the browser but is blind to server-side infections and file uploads. Malware Monitor stops the attack at the moment of upload, inside PHP, before any file is saved — proven on a live PolyShell zero-day that both external services missed.
Real-world numbers from production stores
Magento Stores Protected
Malicious Uploads Blocked
Estimated Threat Variants
Scan Overhead Per Upload
Common questions
Everything you need to know before installing.
No measurable impact. The scan runs synchronously in PHP before the file is saved to disk, but the analysis itself takes microseconds for typical files. On our benchmarks, even a 10 MB file adds less than 5 ms to the upload pipeline. Your customers will not notice anything.
Magento 2.4.x Community Edition and Enterprise Edition, including Adobe Commerce Cloud. Both Shield and Shield Pro are tested against 2.4.4 through 2.4.8. PHP 8.1, 8.2, and 8.3 are supported.
The upload is blocked before the file touches disk. The admin panel shows a real-time alert modal with full forensic detail: filename, MIME type, detected threat pattern, IP address, and endpoint. The event is logged to the Upload Attempts grid and an email alert is sent to configured recipients. No malicious file ever reaches your store.
Shield covers real-time upload interception, pattern detection, auto-quarantine, email alerts, cron-based full store scanning, content threat scanning, and admin dashboard — everything a single store needs. Shield Pro adds IP Firewall with auto-block, database content scanning, CLI tools for CI/CD pipelines, settings change audit log, per-user config password protection, directory extension statistics, and owner-candidate file detection. Pro also covers 3 domains instead of 1 and includes priority support.
Yes — both plans come with a 30-day satisfaction guarantee. If Malware Monitor doesn't work as described on your supported Magento version, contact us first and we'll fix it within 3 business days. If we can't resolve the issue, you get a full refund.
Never. Malware Monitor is 100% on-premise. All scanning logic runs inside your PHP process. No files, hashes, URLs, or telemetry of any kind are sent anywhere. This is the fundamental difference from cloud WAFs and SaaS scanners like Sucuri or Sansec.
PolyShell exploits Magento's unauthenticated REST API file upload endpoint. Malware Monitor intercepts uploads at the PHP Observer level — including the REST API — and scans file content before it is written to disk. It detects PHP code embedded inside seemingly valid image files (polyglot technique), magic-byte mismatches, and MIME spoofing. It caught this attack in the wild months before Adobe released an official patch.
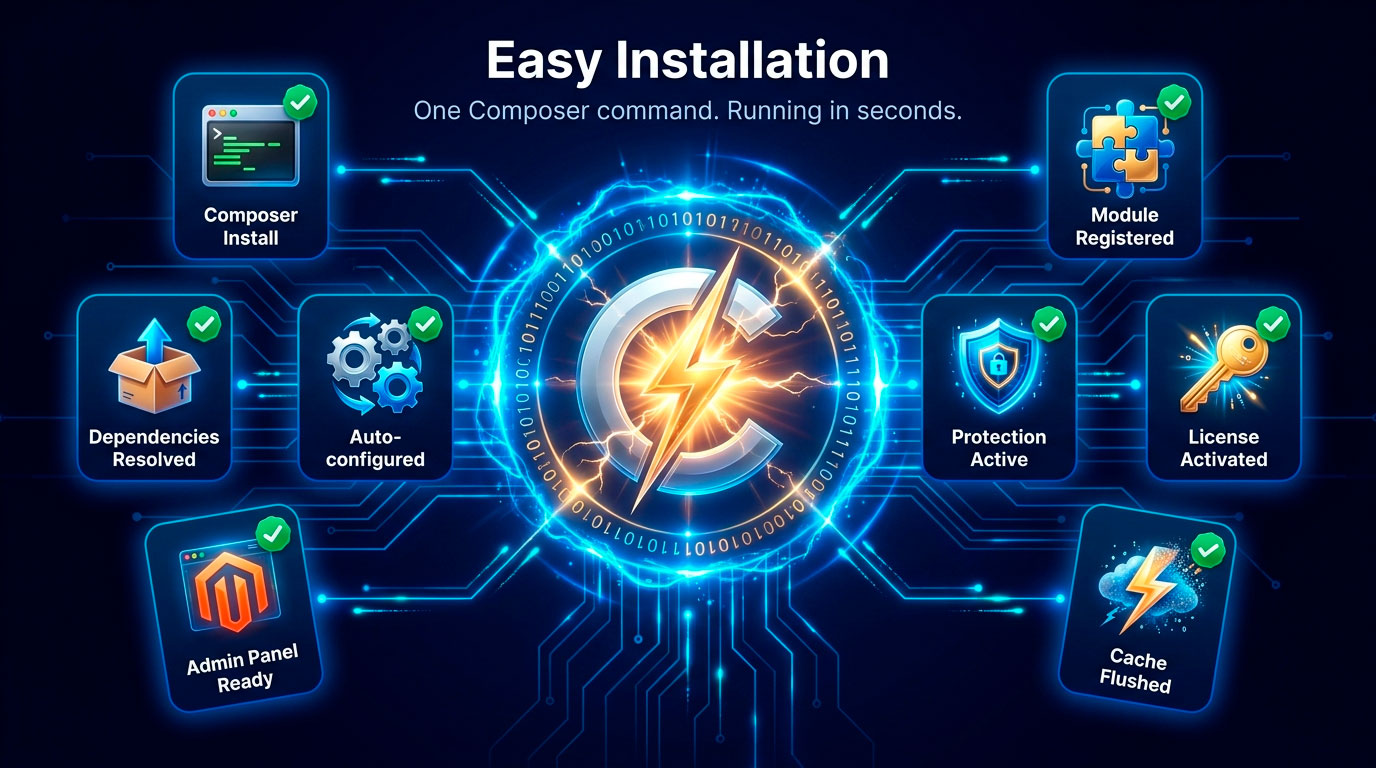
Installation takes under 10 minutes via Composer: composer require magenear/module-malware-monitor, then bin/magento setup:upgrade and bin/magento cache:flush. The module self-registers and begins protecting uploads immediately. A full setup guide is included in the documentation.
Yes. Both Shield and Shield Pro include cron-based full store scanning that periodically walks your file system and reports suspicious files. Shield Pro additionally offers the malware:scan CLI command for on-demand scanning, useful in CI/CD pipelines or post-deployment audits.
Content threat scanning inspects CMS pages, CMS blocks, product descriptions, category descriptions, widgets, email templates, design configuration, and system configuration fields for embedded PHP, JavaScript injections, obfuscated code, and other known payload patterns. Shield detects and alerts; Shield Pro can also block saves that contain detected threats.
Shield covers 1 domain (production store). Shield Pro covers 3 domains — useful for multi-store setups or agencies managing several client stores. Both licenses include staging/development use at no extra cost.
Yes. Malware Monitor is a standard Magento 2 module and is fully compatible with Adobe Commerce Cloud. The on-premise nature of the scanning means no outbound firewall rules are needed, and it passes Adobe's extension quality program requirements.
Stop the next attack
before it happens.
On-premise Magento security. No cloud. No subscription lock-in.
Blocks malware at upload time — before it ever touches disk.